Why is the Cisco 300-425 the hard currency of 2025?
In 2025, wireless networks will no longer be a nice-to-have, but the lifeblood of enterprises. With the popularization of Wi-Fi 6E and the surge in demand for multi-site design, wireless talents have become popular. The Cisco 300-425 ENWLSD certification is not a piece of paper, but a passport to prove that you can master these trends.
This article is no nonsense: it gives you a preparation path from scratch, plus 15 exclusive test questions, so you can get started directly. There are also 226 complete and latest exam questions and answers: https://www.pass4itsure.com/300-425.html to help you pass the exam easily. Whether you are a novice or an old bird, follow this route and 300-425 will be right in front of you.
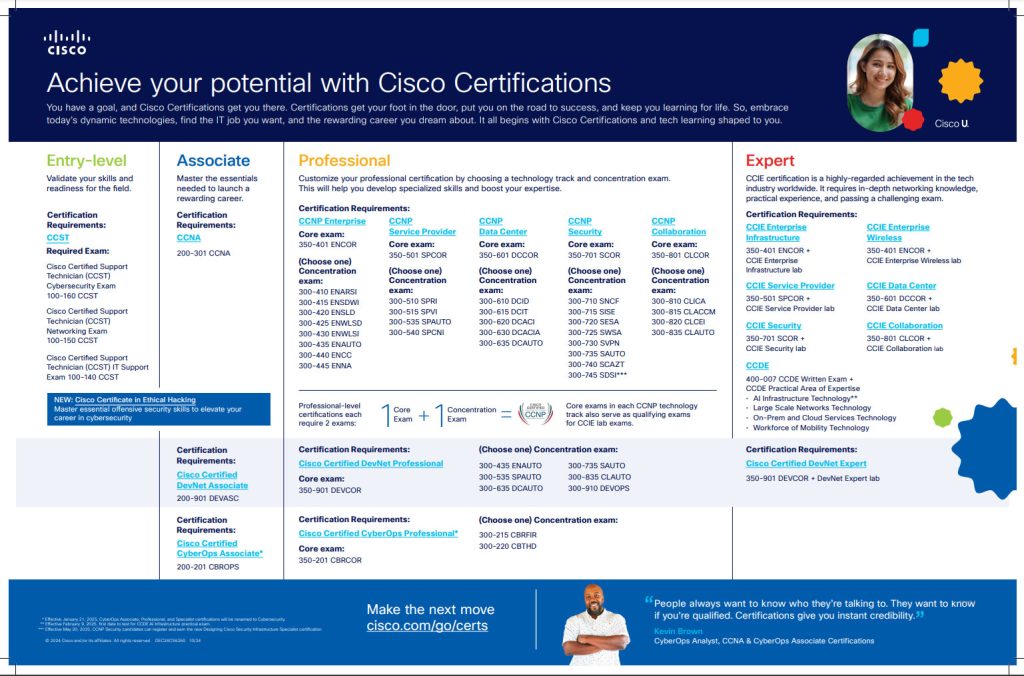
Cisco 300-425 ENWLSD Certification Overview
Certification Snapshot:
Full Name:Designing Cisco Enterprise Wireless Networks (ENWLSD)Target Audience:Tailored for wireless network designers and hardcore IT professionals.Significance:A core piece of the CCNP Enterprise puzzle, a benchmark for professional wireless skills.
Exam Core Breakdown:
Duration: 90 minutes, fast-paced. Question Types: Multiple choice, drag-and-drop, with occasional curveballs.
» Read more about: 2025 Cisco 300-425 ENWLSD Exam Prep Roadmap and Q&As »