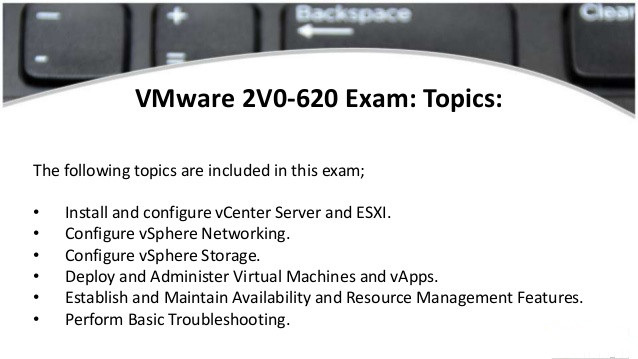
Pass4itsure is the final source of preparation through the VMware 2v0-620 exam.
We offer Practice test questions (1-41) free, pass4itsure frequently updated exam questions and answers, our exam questions come from VMware experts, they review each question and answer the description section to help you understand the concepts and pass the certification exams.
Serious practice is the necessary way to pass the exam.
All of our exam questions are updated at any time, including the latest questions and answers from the VMware 2v0-620 exam.
VMware experts have verified every question and answer on the pass4itsure.
They are trustworthy, they have many years of professional experience and exam subjects. We are committed to providing you with the exact vsphere 6 basic beta exam questions and answers, as well as descriptive explanations.